Rumored Buzz on Risk Management Enterprise
Wiki Article
Not known Details About Risk Management Enterprise
Table of ContentsRisk Management Enterprise for DummiesRisk Management Enterprise - The FactsThe smart Trick of Risk Management Enterprise That Nobody is Discussing
Control that can see or edit these aspects by establishing certain access legal rights for private customers, ensuring details protection and tailored use. Allows individuals to tailor their interface by picking and preparing vital data aspects. Provides a customized experience by permitting modification of where and just how data elements are displayed.It enables access to real-time integrated data quickly. Facilities can use extensive data knowledge for quicker and more enlightened decision-making.
Diligent is a danger management software that allows enhancing efficiency, and increases growth. It additionally assists check risks with ERM software that includes integrated analytics and adapts to your organization demands.
The Definitive Guide to Risk Management Enterprise
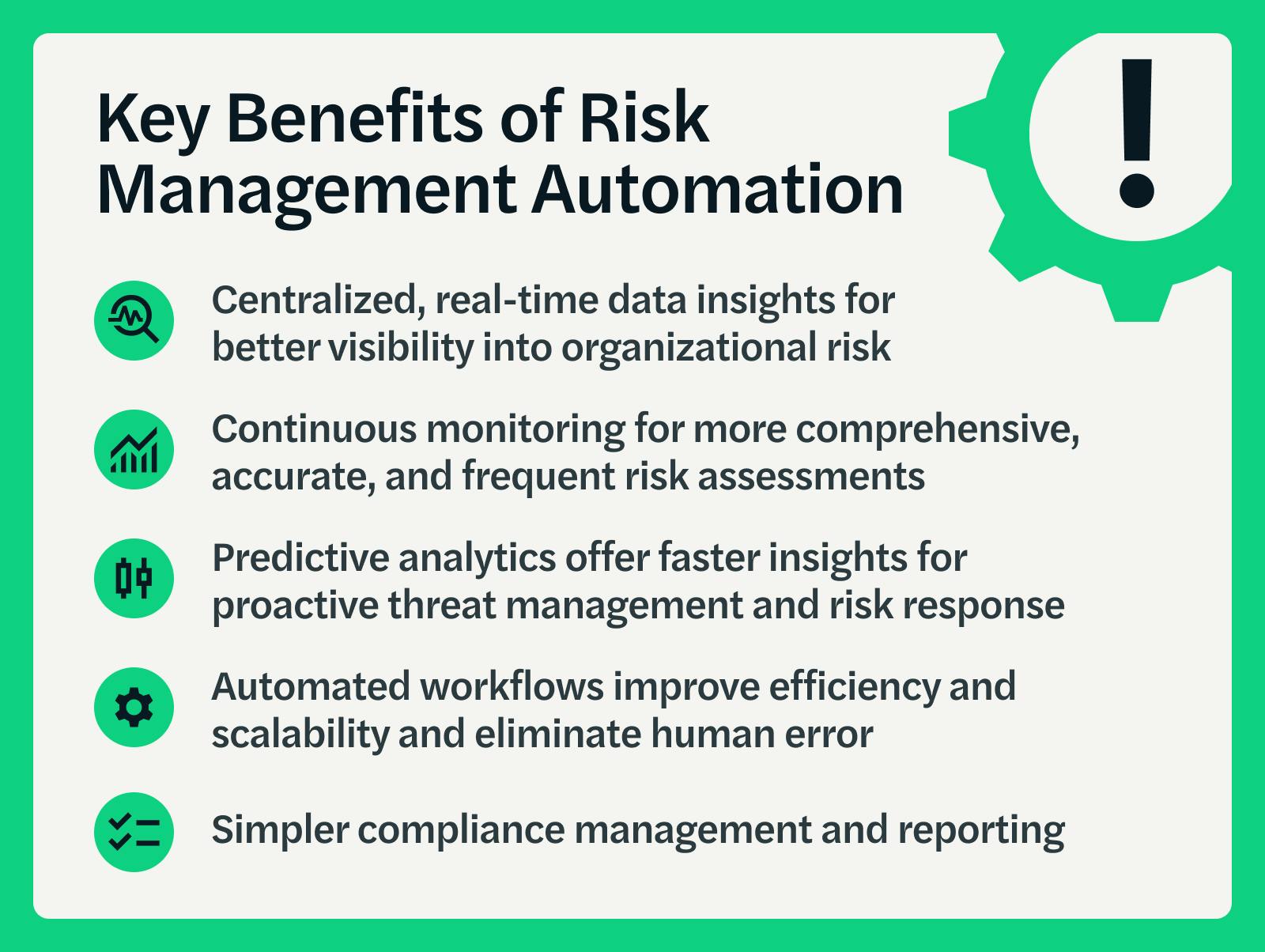
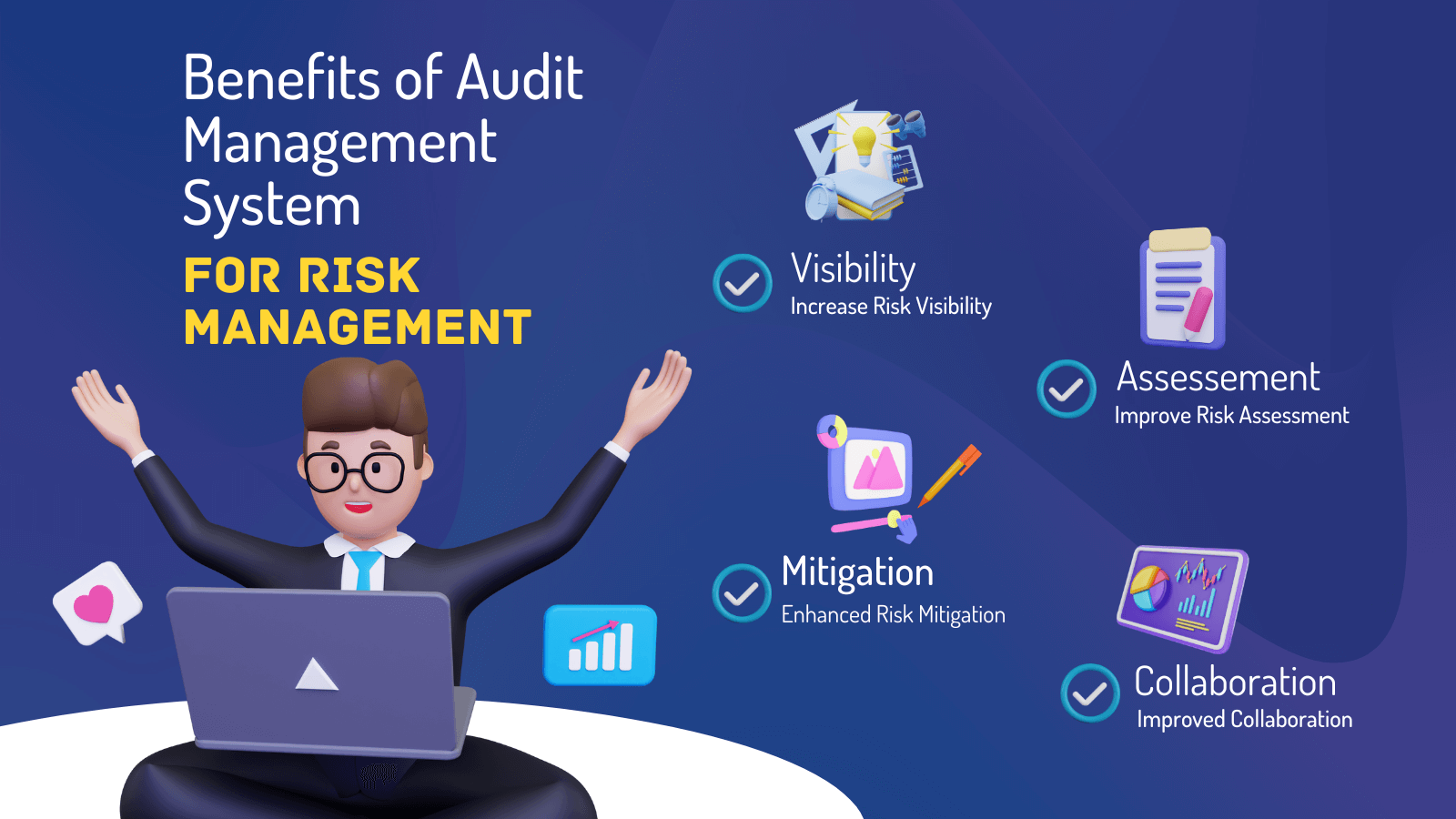
Streamlines the procedure of collecting threat data from different components of the organization. Provides leadership and the board with real-time threat insights. Usage ACL's advanced analytics to find danger patterns and anticipate hazards.This enables business to record threat insights and red flags in the third-party supplier's safety and security record. Makes it possible for companies to record and record threat understandings and red flags in third-party vendor safety records.
Identifying dangers ahead of time aids a facility get ready for audits. It additionally minimizes threat via YOURURL.com structured conformity and danger administration. Because of this facilities won't have to manage different systems for danger monitoring. The individuals of Hyperproof can systematize threat monitoring in one area. It can aid accumulate and track all your risks in the Hyperproof risk register.
It makes sure that everything is arranged and accessible for auditors. Utilizes automation to maintain proof current while decreasing hands-on initiative. It offers quick accessibility to needed info and paperwork. This guarantees the protection of Active evidence instances by allowing multi-factor authentication (MFA) making use of authenticator apps such as Google Authenticator, Microsoft Authenticator, or Authy.
Not known Details About Risk Management Enterprise
It provides top-tier safety and security functions to protect sensitive data. This threat administration software program is an excellent device for centers looking to repair unneeded issues or threats.
Users can additionally use the AI-powered tools and pre-existing material to produce, assess, prioritize, and address risks efficiently. Simplifies the process of setting up and inhabiting danger registers.
Report this wiki page